[[{“value”:”
Android users face a sophisticated security threat as malicious actors increasingly leverage legitimate system features to gain unauthorized access to devices.
A concerning trend has emerged where attackers exploit Original Equipment Manufacturer (OEM) permissions to perform privilege escalation attacks, creating vulnerabilities that bypass conventional security measures.
This attack vector represents a significant evolution in mobile threats, as it utilizes seemingly legitimate channels rather than relying solely on traditional exploit techniques.
The threat operates by acquiring excessive privileges through mechanisms that appear legitimate to both users and security systems.
These include sideloaded applications that circumvent Google Play Store security checks and applications pre-installed by device manufacturers that come with elevated privileges.
What makes these attacks particularly dangerous is their ability to operate without triggering standard detection systems, as they use permissions that are technically legitimate when viewed individually.
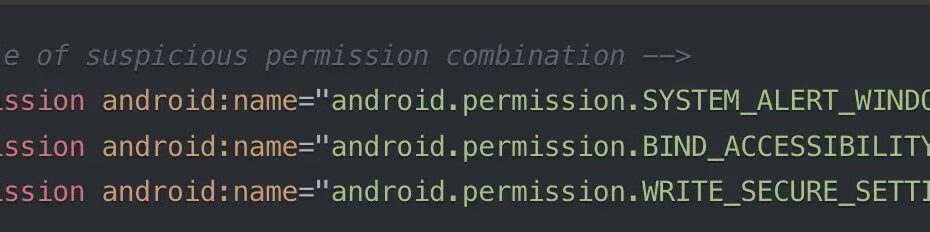
Zimperium security researchers identified that these attacks often combine multiple permissions that, while innocuous in isolation, create dangerous capabilities when used together.
.webp)
Their analysis revealed that applications requesting combinations of system-level permissions can effectively take control of devices without exploiting conventional security vulnerabilities.
The impact of these attacks extends beyond individual users to enterprise environments, where compromised devices can serve as entry points to broader network infrastructure.
Once attackers gain privileged access to a device, they can intercept sensitive data, capture authentication credentials, and potentially pivot to connected systems.
The stealth nature of these attacks makes them particularly concerning for organizations with Bring Your Own Device (BYOD) policies.
Device manufacturers inadvertently contribute to the problem by including proprietary permissions that grant extensive system access, bypassing Android’s standard security model.
For example, certain OEM permissions allow applications to modify security policies and gain hardware-level access, creating opportunities for malicious exploitation.
Infection Mechanism Through Accessibility API Abuse
The primary infection vector leverages Android’s Accessibility API, a powerful tool originally designed to assist users with disabilities.
Malicious applications request access to this API, which allows them to read screen contents and perform inputs on behalf of the user.
Once granted, attackers can monitor user interactions, capture sensitive information, and automate actions without user awareness.
To bypass Android’s “Restricted Settings” protection mechanism, attackers employ a sophisticated technique using session-based installation methods.
.webp)
While Android 13 implemented restrictions on Accessibility API access for sideloaded apps, malicious actors circumvent this by using the session-based installation method typically used by legitimate app stores. The following code pattern is often identified in these malicious applications:
InMemoryDexClassLoader loader = new InMemoryDexClassLoader(
ByteBuffer.wrap(dexBytes),
getClassLoader()
);This code snippet demonstrates how malicious applications dynamically load executable code after installation, effectively hiding their true functionality until after security checks are complete.
.webp)
Zimperium’s application vetting process identified several cleaner apps with millions of downloads collectively that exhibited this behavior, loading malicious code from command-and-control servers that transformed seemingly legitimate applications into banking trojans.
The attackers specifically target combinations of permissions including SYSTEM_ALERT_WINDOW for drawing overlays, ACCESSIBILITY_SERVICE for monitoring user actions, and WRITE_SECURE_SETTINGS for modifying system settings.
Together, these permissions enable the malware to display fake UI elements, capture user credentials, and change system settings without user awareness.
Automate threat response with ANY.RUN’s TI Feeds—Enrich alerts and block malicious IPs across all endpoints -> Request full access
The post Threat Actors Exploits OEM Permissions on Android Devices to Perform Privilege Escalation Attacks appeared first on Cyber Security News.
“}]]
Read More .webp) Cyber Security News
Cyber Security News