[[{“value”:”
Windows Shortcut (LNK) files, traditionally used for creating quick access links to applications and files, have emerged as a prominent attack vector in the cybersecurity landscape.
These seemingly innocuous files, identifiable by their small arrow icon overlay, are increasingly being weaponized by threat actors to execute malicious payloads while maintaining a facade of legitimacy.
The flexibility and ubiquity of LNK files across Windows environments make them attractive for cybercriminals seeking to bypass traditional security measures.
The malicious exploitation of LNK files has reached concerning levels, with cybersecurity researchers observing a dramatic increase in their weaponization.
These files leverage Windows’ built-in functionality to execute commands, download payloads, and establish persistence on compromised systems.
The attack methodology often involves disguising malicious LNK files as legitimate documents by manipulating their icons and filenames to appear trustworthy to potential victims.
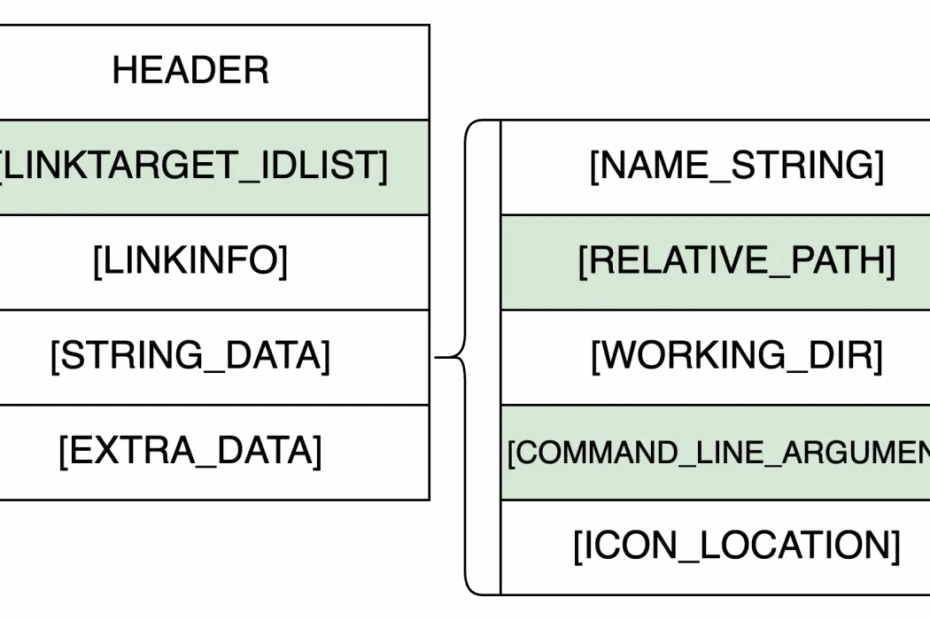
Palo Alto Networks analysts identified four distinct categories of LNK malware through comprehensive analysis of 30,000 malicious samples.
.webp)
Their research revealed that threat actors have systematically organized their approaches into LNK exploits, malicious file execution, in-argument script execution, and overlay content execution techniques.
This categorization demonstrates the sophisticated evolution of LNK-based attacks and the diverse methodologies employed by cybercriminals.
.webp)
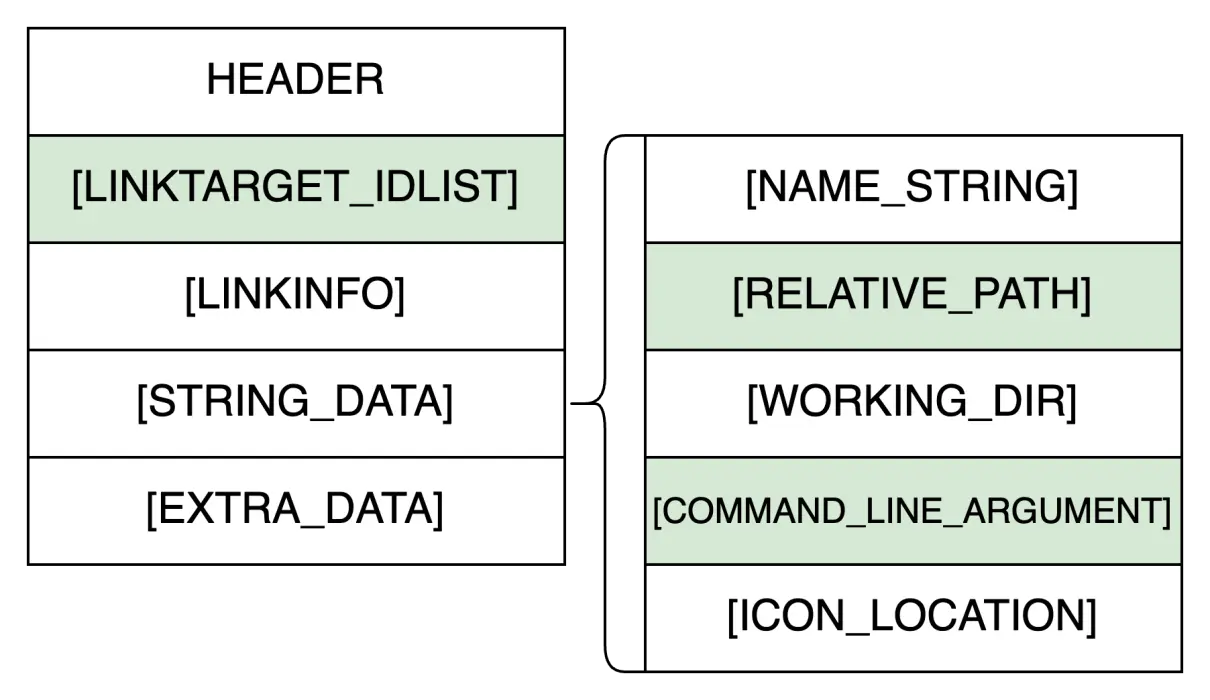
The research findings indicate that PowerShell and Command Prompt serve as the primary execution vehicles for LNK malware, accounting for over 80% of all system target utilization.
Specifically, powershell.exe is leveraged in 59.4% of cases, while cmd.exe is utilized in 25.7% of malicious samples. This heavy reliance on native Windows utilities enables attackers to execute payloads without requiring additional tools.
In-Argument Script Execution: The Dominant Attack Vector
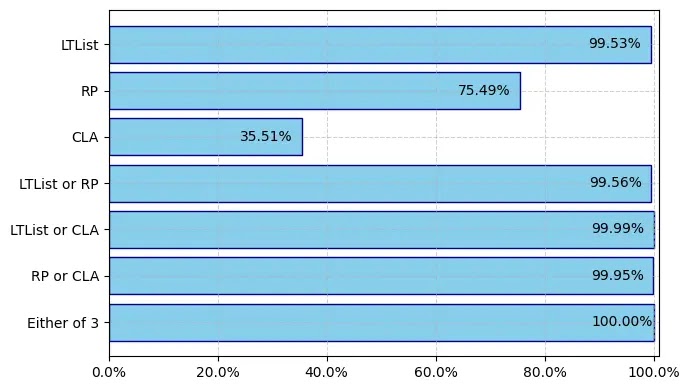
In-argument script execution represents one of the most prevalent techniques employed by LNK malware operators.
This method involves embedding malicious scripts directly within the COMMAND_LINE_ARGUMENTS field of the LNK file, effectively transforming the shortcut into a delivery mechanism for malicious payloads.
The technique exploits the inherent trust users place in shortcut files while leveraging Windows’ command-line interpreters.
.webp)
The implementation often involves Base64 encoding to obfuscate malicious content. A typical PowerShell command structure appears as:-
powershell.exe -Nonl -W Hidden -NoP -Exec Bypass -EncodedCommand [Base64_String]When decoded, these commands frequently contain instructions to download malicious DLLs from remote servers and execute secondary payloads.
The sophistication is enhanced through obfuscation techniques including command assembling and strategic use of Windows environment variables.
Investigate live malware behavior, trace every step of an attack, and make faster, smarter security decisions -> Try ANY.RUN now
The post Weaponization of LNK Files Surge by 50% and Primarily Used in Four Different Malware Categories appeared first on Cyber Security News.
“}]]
Read More .webp) Cyber Security News
Cyber Security News