[[{“value”:”
In today’s digital-first business landscape, advanced endpoint security is not just a luxury it’s a necessity.
As organizations expand their operations across cloud, remote, and hybrid environments, every endpoint becomes a potential target for cybercriminals.
From sophisticated ransomware to zero-day exploits, the threats are evolving at an unprecedented pace. Selecting the right endpoint security tool can mean the difference between a minor incident and a devastating breach.
This comprehensive guide reviews the 10 best advanced endpoint security tools for 2024, focusing on their cutting-edge features, usability, and real-world performance.
We’ve evaluated each solution for its ability to protect against modern threats, integrate with existing systems, and provide actionable insights to security teams.
Whether you’re a small business or a global enterprise, this article will help you make an informed decision to secure your endpoints and safeguard your data.
Primary SEO Keywords:
- Advanced endpoint security tools
- Endpoint protection platforms
- Endpoint detection and response (EDR)
- Best endpoint security software
Secondary SEO Keywords:
- Cybersecurity solutions
- Ransomware protection
- Threat intelligence
- Zero-day attack defense
Comparison Table: Top 10 Advanced Endpoint Security Tools (2024)
| Tool Name (Official Site) | AI/ML Protection | EDR Capabilities | Cloud Support | Ransomware Defense |
|---|---|---|---|---|
| CrowdStrike Falcon | Yes | Yes | Yes | Yes |
| SentinelOne Singularity | Yes | Yes | Yes | Yes |
| Microsoft Defender for Endpoint | Yes | Yes | Yes | Yes |
| Trend Micro Vision One | Yes | Yes | Yes | Yes |
| Bitdefender GravityZone | Yes | Yes | Yes | Yes |
| Cisco Secure Endpoint | Yes | Yes | Yes | Yes |
| Sophos Intercept X | Yes | Yes | Yes | Yes |
| Trellix Endpoint Security | Yes | Yes | Yes | Yes |
| ESET Protect Enterprise | Yes | Yes | Yes | Yes |
| Malwarebytes ThreatDown | Yes | Yes | Yes | Yes |
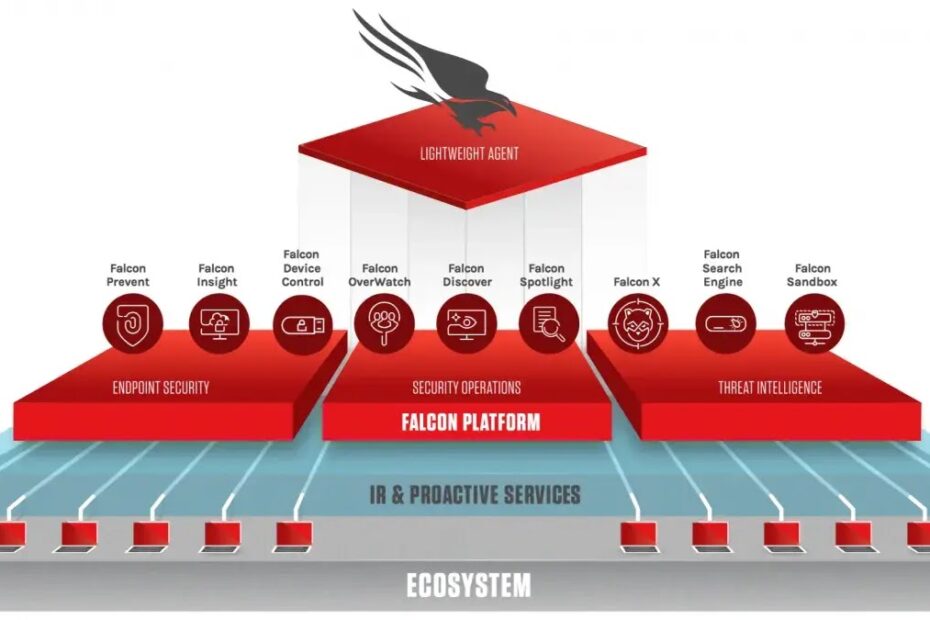
1. CrowdStrike Falcon
.webp)
CrowdStrike Falcon is a leader in cloud-native endpoint protection, offering unparalleled visibility and control across all devices.
Its lightweight agent ensures minimal impact on system performance while delivering robust protection against malware, ransomware, and advanced persistent threats.
The platform leverages AI-driven threat intelligence and behavioral analytics to detect and stop threats in real time, even those that evade traditional security solutions.
Falcon’s cloud-based architecture allows for rapid deployment and seamless scalability, making it ideal for organizations of any size.
Security teams benefit from automated investigations and response, reducing the time to remediate incidents and minimizing business disruption.
Key Features
- AI-powered threat detection and response
- Real-time endpoint visibility and analytics
- Integrated threat intelligence feeds
- Automated investigation and remediation workflows
| Pros | Cons |
|---|---|
| Minimal system impact | Premium pricing |
| Fast, cloud-native deployment | Learning curve for new users |
| Excellent threat intelligence | Advanced features require training |
| Automated response capabilities | May require integration with other tools |
2. SentinelOne Singularity
.webp)
SentinelOne Singularity delivers autonomous endpoint protection powered by advanced AI and machine learning.
The platform excels at detecting, preventing, and responding to threats across endpoints and cloud workloads with minimal human intervention.
Its behavioral analytics engine identifies suspicious activity in real time, while automated rollback features help recover from ransomware attacks instantly.
SentinelOne’s unified console simplifies management, providing deep visibility and actionable insights for security teams.
The solution is highly scalable, making it suitable for both growing businesses and large enterprises seeking comprehensive endpoint security.
Key Features
- Autonomous AI-driven detection and response
- Behavioral analytics for real-time threat identification
- Automated ransomware rollback
- Unified management console for all endpoints
| Pros | Cons |
|---|---|
| Fully automated workflows | Can be resource-intensive during scans |
| Real-time detection and response | Advanced setup may require expertise |
| Strong rollback after ransomware | Premium features may cost extra |
| Scalable for all business sizes | Interface can be complex for new users |
3. Microsoft Defender for Endpoint
.webp)
Microsoft Defender for Endpoint is a comprehensive security platform that integrates seamlessly with the Microsoft ecosystem.
Designed for organizations leveraging Microsoft 365 and Azure, it combines endpoint protection, EDR, threat intelligence, and vulnerability management in a single solution.
Defender uses AI and automation to detect and respond to threats across Windows, macOS, Linux, and mobile devices.
Its cloud-based management enables rapid deployment and policy enforcement, while built-in XDR capabilities provide extended visibility across the IT environment.
Key Features
- Seamless integration with Microsoft products
- AI-enhanced detection and response
- Cross-platform support (Windows, Mac, Linux, mobile)
- Built-in vulnerability and threat management
| Pros | Cons |
|---|---|
| Excellent for Microsoft environments | Less ideal for mixed OS setups |
| Strong AI-driven detection | Requires tuning to reduce false positives |
| Affordable for existing Microsoft users | Some features only in higher tiers |
| Cloud-native deployment | May lack depth for advanced threat hunting |
4. Trend Micro Vision One
.webp)
Trend Micro Vision One offers advanced endpoint security with integrated XDR capabilities, correlating activities across endpoints, servers, email, and cloud workloads.
Its behavioral analytics engine provides early detection of suspicious behaviors, while the cloud-based platform ensures scalability and centralized management.
Vision One is designed for organizations seeking comprehensive protection against modern threats, including ransomware, fileless malware, and targeted attacks.
The platform’s intuitive dashboard and automated response features empower security teams to act quickly and efficiently.
Key Features
- Cross-platform XDR integration
- Behavioral analytics for early threat detection
- Cloud-based management and scalability
- Automated incident response capabilities
| Pros | Cons |
|---|---|
| Excellent threat correlation | Interface can be complex for new users |
| Strong behavioral analytics | Advanced features in higher tiers |
| Scalable cloud platform | Initial setup may be time-consuming |
| Automated response workflows | May require training for full utilization |
5. Bitdefender GravityZone

Bitdefender GravityZone is renowned for its robust machine learning and signature-based threat detection.
The platform delivers comprehensive protection against known and unknown threats, combining EDR, risk analytics, and network attack defense.
GravityZone’s lightweight agent ensures minimal performance impact, making it suitable for organizations prioritizing speed and efficiency.
Flexible deployment options cloud or on-premises allow businesses to tailor the solution to their specific needs.
Its intuitive management console simplifies policy enforcement and threat monitoring across all endpoints.
Key Features
- Machine learning and signature-based detection
- Integrated EDR and risk analytics
- Lightweight agent for minimal impact
- Flexible cloud or on-premises deployment
| Pros | Cons |
|---|---|
| Strong detection capabilities | Reporting interface could improve |
| Minimal system performance impact | Complex configuration for small teams |
| Flexible deployment options | Advanced analytics may require expertise |
| Easy policy management | Some features only in premium plans |
6. Cisco Secure Endpoint
.webp)
Cisco Secure Endpoint (formerly AMP for Endpoints) delivers advanced detection, prevention, and response capabilities through a cloud-native platform.
Leveraging Cisco’s global threat intelligence, it provides real-time visibility into threats and automates incident response with playbooks.
The platform integrates seamlessly with Cisco’s broader security ecosystem, offering unified management and deep behavioral analytics.
Designed for organizations with complex security requirements, Cisco Secure Endpoint helps reduce remediation times and improves overall cyber resilience.
Key Features
- Cloud-native management and deployment
- Integrated threat intelligence from Cisco Talos
- Automated response with playbooks
- Deep behavioral analytics for threat detection
| Pros | Cons |
|---|---|
| Strong integration with Cisco tools | Can be overwhelming for new users |
| Excellent behavioral analytics | Licensing can be complex |
| Automated incident response | May require Cisco expertise |
| Scalable for large enterprises | Initial setup may be lengthy |
7. Sophos Intercept X
.webp)
Sophos Intercept X leverages deep learning AI to provide advanced endpoint protection against both known and unknown threats.
Its CryptoGuard technology prevents ransomware attacks by detecting and stopping suspicious encryption activities.
Intercept X combines EDR, exploit prevention, and active adversary mitigations in a single solution, making it ideal for organizations facing complex attack techniques.
The user-friendly interface and automated workflows simplify security management, even for teams with limited resources.
Key Features
- Deep learning malware detection
- CryptoGuard anti-ransomware technology
- Exploit prevention and active adversary mitigation
- Integrated EDR for threat analysis and response
| Pros | Cons |
|---|---|
| Strong ransomware protection | Advanced features may require training |
| User-friendly interface | Some features only in higher tiers |
| Comprehensive incident response | May be resource-intensive during scans |
| Easy deployment and management | Reporting could be more detailed |
8. Trellix Endpoint Security
.webp)
Trellix Endpoint Security combines real-time threat intelligence, machine learning, and behavior-based analytics to protect against advanced attacks.
Its MalwareGuard engine detects and blocks emerging threats, while automated incident response features minimize damage by isolating infected endpoints.
Trellix offers integrated EDR capabilities, providing comprehensive visibility and control over endpoint threats.
The platform is particularly suited for high-security sectors like finance and healthcare, where advanced behavioral analytics are critical.
Key Features
- Real-time threat intelligence and machine learning
- Behavior-based analytics for anomaly detection
- Automated incident response and endpoint isolation
- Integrated EDR for comprehensive threat visibility
| Pros | Cons |
|---|---|
| Advanced behavioral analytics | May require expertise for configuration |
| Automated incident response | Reporting features could improve |
| Strong for high-security sectors | Lacks some advanced threat hunting tools |
| Integrated EDR capabilities | Licensing can be complex |
9. ESET Protect Enterprise
.webp)
ESET Protect Enterprise is designed for organizations seeking multilayered endpoint security with strong detection and management capabilities.
Leveraging machine learning, ESET provides real-time visibility into endpoint status and vulnerabilities.
The platform offers flexible deployment options cloud or on-premises and an intuitive management console for policy enforcement.
ESET’s low resource consumption makes it ideal for performance-focused environments, while its robust policy management features streamline security operations.
Key Features
- Machine learning-powered threat detection
- Real-time endpoint status and vulnerability visibility
- Flexible cloud or on-premises deployment
- Intuitive, easy-to-use management console
| Pros | Cons |
|---|---|
| Low resource consumption | Reporting features could be more detailed |
| Flexible deployment options | Lacks advanced threat hunting tools |
| Easy policy management | Some features only in premium plans |
| Real-time visibility | May not suit very large enterprises |
10. Malwarebytes ThreatDown
.webp)
Malwarebytes ThreatDown (formerly Malwarebytes EDR) offers a streamlined endpoint security solution with a focus on simplicity and speed.
Its single-agent architecture makes deployment and management easy, especially for small and mid-sized teams.
ThreatDown provides robust protection against ransomware, malware, and suspicious activity, with fast detection and response capabilities.
The platform is known for its effectiveness in cleaning up infected systems and minimizing IT overhead, making it a popular choice for organizations with limited security resources.
Key Features
- Single-agent, easy deployment and management
- Fast detection and response to threats
- Robust ransomware and malware protection
- Minimal IT overhead for small teams
| Pros | Cons |
|---|---|
| Easy to deploy and manage | Advanced features in higher-tier plans |
| Fast response capabilities | Lacks XDR integration |
| Effective malware cleanup | Limited advanced threat hunting |
| Good for small/mid-sized teams | May not scale for large enterprises |
Conclusion
Choosing the right advanced endpoint security tool is critical for protecting your organization against today’s sophisticated cyber threats.
Each solution reviewed here offers unique strengths, from AI-driven detection and automated response to seamless integration and user-friendly management.
CrowdStrike Falcon and SentinelOne Singularity lead the pack with their autonomous protection and real-time analytics, while Microsoft Defender for Endpoint stands out for organizations deeply invested in the Microsoft ecosystem.
Trend Micro Vision One and Bitdefender GravityZone provide robust, scalable options for businesses of all sizes, and Cisco Secure Endpoint excels in environments requiring deep integration and advanced analytics.
Sophos Intercept X and Trellix Endpoint Security are ideal for organizations facing complex attack vectors, offering comprehensive EDR and behavioral analytics.
ESET Protect Enterprise and Malwarebytes ThreatDown round out the list with their ease of use and performance-focused design, making them excellent choices for smaller teams or those with limited IT resources.
In 2024, the best endpoint security solutions are defined by their ability to adapt, automate, and provide actionable intelligence.
By investing in one of these top tools, you can ensure your endpoints—and your business—are protected against both current and emerging threats.
Always consider your organization’s unique needs, infrastructure, and growth plans when selecting a solution, and stay proactive in your cybersecurity strategy to stay ahead of the threat landscape.
The post 10 Best Advanced Endpoint Security Tools – 2025 appeared first on Cyber Security News.
“}]]
Read More .webp) Cyber Security News
Cyber Security News