[[{“value”:”
The brief lull following May’s multinational takedown of the Lumma Stealer infrastructure proved deceptive.
Within weeks, telemetry again lit up with fresh command-and-control (C2) beacons, revealing that the information-stealing malware had swapped overt marketplace promotion for quieter channels while expanding its victim base.
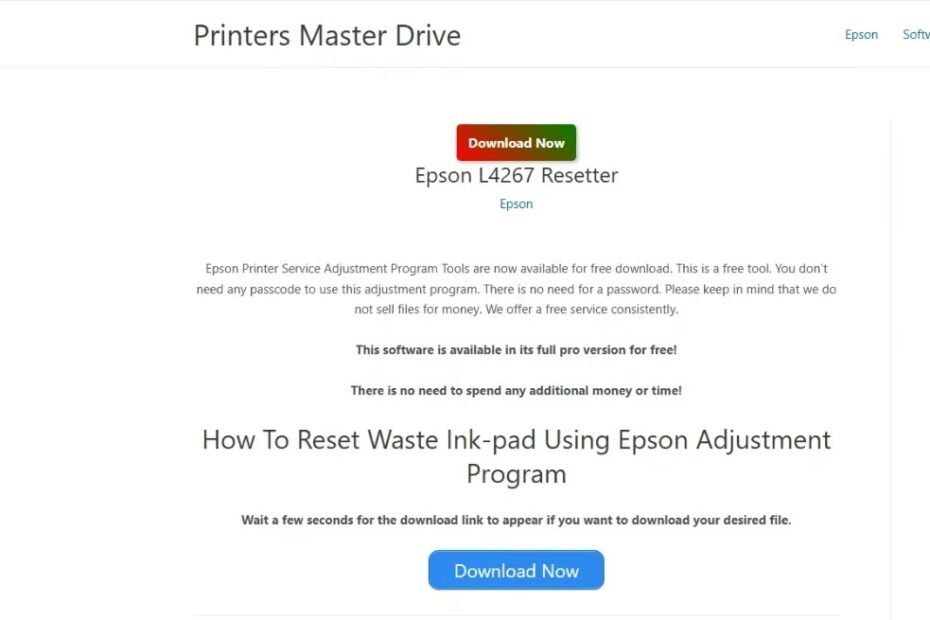
In its new incarnation, Lumma is most often packaged inside counterfeit installers for sought-after software, luring users who search for “cracks,” “keygens,” or game cheats into downloading the Trojan instead of the promised free tool.
.webp)
Once a victim lands on one of these fraudulent portals, JavaScript silently redirects the browser through a traffic distribution system that fingerprints the host.
If hardware, locale, and security controls look profitable, the site serves a password-protected ZIP containing an innocuous-looking executable or PowerShell script engineered to bootstrap Lumma Stealer, all while evading casual inspection.
Trend Micro researchers noted that June and July telemetry showed a rebound to pre-takedown volumes of targeted accounts, underlining both the malware’s resilience and the scale of users still hunting for pirated apps.
Trend Micro analysts also identified a parallel push on GitHub and social platforms: automatically generated repositories advertise “HWID spoofers” or “Photoshop 2025 full crack,” yet the only release asset is the Lumma payload.
.webp)
YouTube videos and Facebook posts amplify these links, instructing viewers to disable antivirus before installation—a social-engineering touch that further stacks the odds in attackers’ favor.
The consequences are severe, as they once executed, Lumma harvests browser cookies, crypto-wallet files, and cloud-storage session tokens, then exfiltrates them via an encrypted C2 channel.
Corporate accounts protected by multifactor authentication are not immune; stolen cookies often bypass login prompts, giving intruders immediate access to email, collaboration portals, or source-code repositories.
Infection Mechanism: Memory-Only Payload Delivery
The current campaigns favor a file-less approach that frustrates endpoint detection logic tuned to disk artefacts.
In ClickFix-style drives, compromised websites swap their normal content for a bogus CAPTCHA page.
Victims are told to press Win + R and run a single-line PowerShell command, unwittingly spawning an in-memory loader that performs an XOR decrypt of an embedded .NET assembly—Lumma itself—then calls its entry point without ever touching the filesystem.
.webp)
A condensed excerpt illustrates the core routine:-
$xorKey = [Convert]::FromBase64String("Q0YwbG5IaUY4YmpEdw==")
$enc = 0x0E,0x10,0xA0,0x6C,0x60,0x48,0x69,0x46
$buf = New-Object byte[] $enc.Length
for ($i=0;$i -lt $enc.Length;$i++){
$buf[$i] = $enc[$i] -bxor $xorKey[$i % $xorKey.Length]
}
[Reflection.Assembly]::Load($buf).EntryPoint.Invoke($null,@())Because no executable is dropped, traditional anti-virus scanners that rely on hash-based signatures rarely trigger.
Network inspection fares little better: C2 domains rotate through lesser-known Russian hosting providers such as Selectel, sidestepping earlier Cloudflare takedown vectors while still enjoying TLS camouflage.
Ultimately, Lumma’s resurgence shows that supply-chain style malvertising and memory-resident loaders can keep a MaaS operation alive even after sweeping infrastructure seizures.
Security teams must combine user education about pirated software with behavioral telemetry that flags suspicious child-process creation and outbound TLS beacons to unfamiliar domains if they hope to close the window that Lumma Stealer so deftly exploits.
Boost detection, reduce alert fatigue, accelerate response; all with an interactive sandbox built for security teams -> Try ANY.RUN Now
The post Lumma Stealer Via Fake Cracked Software Steals Login Credentials and Private Files appeared first on Cyber Security News.
“}]]
Read More .webp) Cyber Security News
Cyber Security News